The use of automation has fundamentally changed the IT landscape and made us more efficient in managing our increasingly complex environments. In this post I will explore the benefits and risks with increasing automation and how these risks can be mitigated with proper auditing, risk management and planning.
Automation comes with a price: We as Auditors(CISAs, QSAs, PCI ISAs, etc.) who we rely upon to be our ethical regulatory compass ensuring that our people, processes and technology are compliant and secure, need to re-think our mindsets and methodologies. We, as auditors, need to make sure that the Agile and Lean #DevOps cultures we build and the tools we use are deployed and used in secure and compliant ways. We need to help the business to be more effective while maintaining security across the enterprise.

So how do we need to improve auditing automation and what do we need to do differently? What auditing challenges does automation bring to the enterprise?
Automation enables organisations to rapidly and consistently provision, configure and deploy servers and applications and infrastructures in ways that has not been possible before. This means that Infrastructure standards are easier to maintain and configuration drift is effortlessly detected, analyzed and mitigated. This is good news for security and infrastructure components can be reliably assessed for security and compliance.
However, with great power comes great responsibility and although automation brings a long needed improvements to our environments it also brings new risks. Protecting the repositories that hold our infrastructure configurations and code is paramount. Protecting the tools that run our continuous integration, delivery and deployment pipelines is crucial. Protecting our developers, sysadmins and personnel tasked with developing and managing our infrastructures ia key.
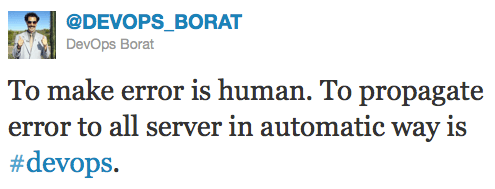
We need to start focusing our audits on automation and understand how the security of automation infrastructure, tools and processes affect our security posture so that we can ensure that we don’t propagate errors, weaknesses and malicious mayhem into our automated environments. We don’t want Continuous Integration to become Continuous Intrusion.
We, the security experts and auditors, need to understand the business and the automation processes and tools that are used so that we can help identify and remediate the risks and weaknesses that come with using them. We need embrace automation so that we know it inside out and can help the business and Devops teams to deliver value while maintaining and improving security. We need to make sure our software and infrastructure is #rugged, that we build in security and not bolt it on in the last sprint, that we audit and assess the stuff that matters in the world of automation.
So go learn tools like Jenkins, GoCd, Concourse, Ansible, Puppet, Chef and Gauntlt so that you know what must be assessed and and how it can be done. Then use that knowledge to help developers and sysadmins secure your automated environments and help your business win!